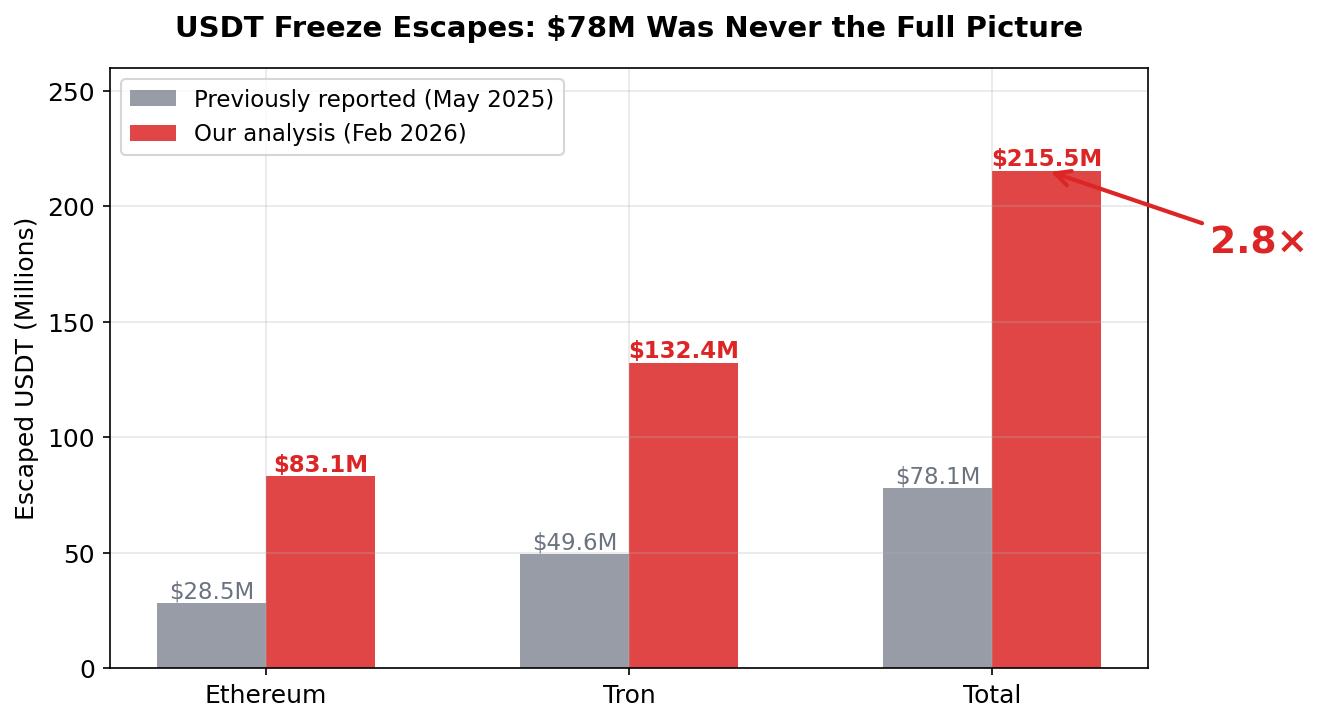
TL;DR: A widely cited report put USDT freeze escapes at $78M. We analyzed all 8,310 executed freeze proposals on Ethereum and Tron — the real number is $215.5M. 2025 alone: $141.7M. The largest single escape: $37.3M moved in under 6 minutes. 18 escapes happened within 60 seconds of proposal submission. The freeze gap is a known, actively exploited vulnerability — and it’s getting worse.
Last May, a widely cited report put the USDT freeze escape figure at $78 million. Decrypt, CoinCentral, and dozens of other outlets ran with it. Tether’s response: the number “should be put in context of the more than $2.7 billion in USDT that Tether has successfully frozen and blocked to date.”
$78 million was never the full picture.
We analyzed every single executed addBlackList proposal on both Ethereum and Tron — 8,310 proposals from 2017 through February 14, 2026 — and cross-validated the results in both Python and Go. The real number: $215.5 million.
2.8x higher. And 2025 alone accounts for $141.7 million — more than all previous years combined.
What We Mean by “Escape”
Let’s be precise about what we’re measuring.
Tether’s USDT contract uses a multisig governance model. Freezing an address happens in two steps:
- Proposal submission: An
addBlackListtransaction is submitted to the multisig contract. Visible on-chain immediately. - Proposal execution: After enough signers approve, the freeze takes effect. Only then does the address lose the ability to transfer USDT.
The gap between step 1 and step 2 — we call it the “freeze gap.” (For a detailed breakdown of this mechanism, see our previous analysis.)
Our definition of escape is strict: any USDT transfer where the from_address matches the target of a freeze proposal, occurring after the proposal was submitted but before it was executed. We exclude address-poisoning dust transfers. We count only outgoing transfers.
Out of 8,310 executed freeze proposals, 8,301 had a measurable delay between submission and execution. Nine were executed in the same block. Of those 8,301, 449 proposals (5.4%) saw at least one escape transfer during the freeze gap.
The Full Picture: $215.5 Million
| Ethereum | Tron | Combined | |
|---|---|---|---|
| Total escaped | $83.1M | $132.4M | $215.5M |
| Proposals with escapes | 102 | 347 | 449 |
| Escape transfers | 296 | 7,208 | 7,504 |
| Escape rate | 3.7% | 6.2% | 5.4% |
Tron dominates in both volume and escape count. No surprise — in 2025, Tron accounted for 84% of all freeze proposals.
How Our Numbers Compare
The $78.1M figure (ETH $28.5M + Tron $49.6M) covered November 2017 through May 2025, analyzing roughly 3,480 wallets primarily on Tron. We extend through February 2026, cover both chains comprehensively, and include all 8,310 proposals.
The gap isn’t just about the extra 9 months. Our methodology captures more escape events because we analyze every proposal individually rather than sampling wallets. The result: higher numbers across every dimension.
Year by Year: The Escape Trend
| Year | ETH Escaped | Tron Escaped | Total | Escape Rate |
|---|---|---|---|---|
| 2021 | $6.15M | ~$4 | $6.15M | 4.6% |
| 2022 | $6.32M | $0.90M | $7.21M | 2.0% |
| 2023 | $6.21M | $11.32M | $17.54M | 5.7% |
| 2024 | $7.92M | $28.89M | $36.81M | 5.2% |
| 2025 | $56.44M | $85.30M | $141.75M | 6.2% |
| 2026 (Jan-Feb) | $0.03M | $5.97M | $6.00M | 6.5% |
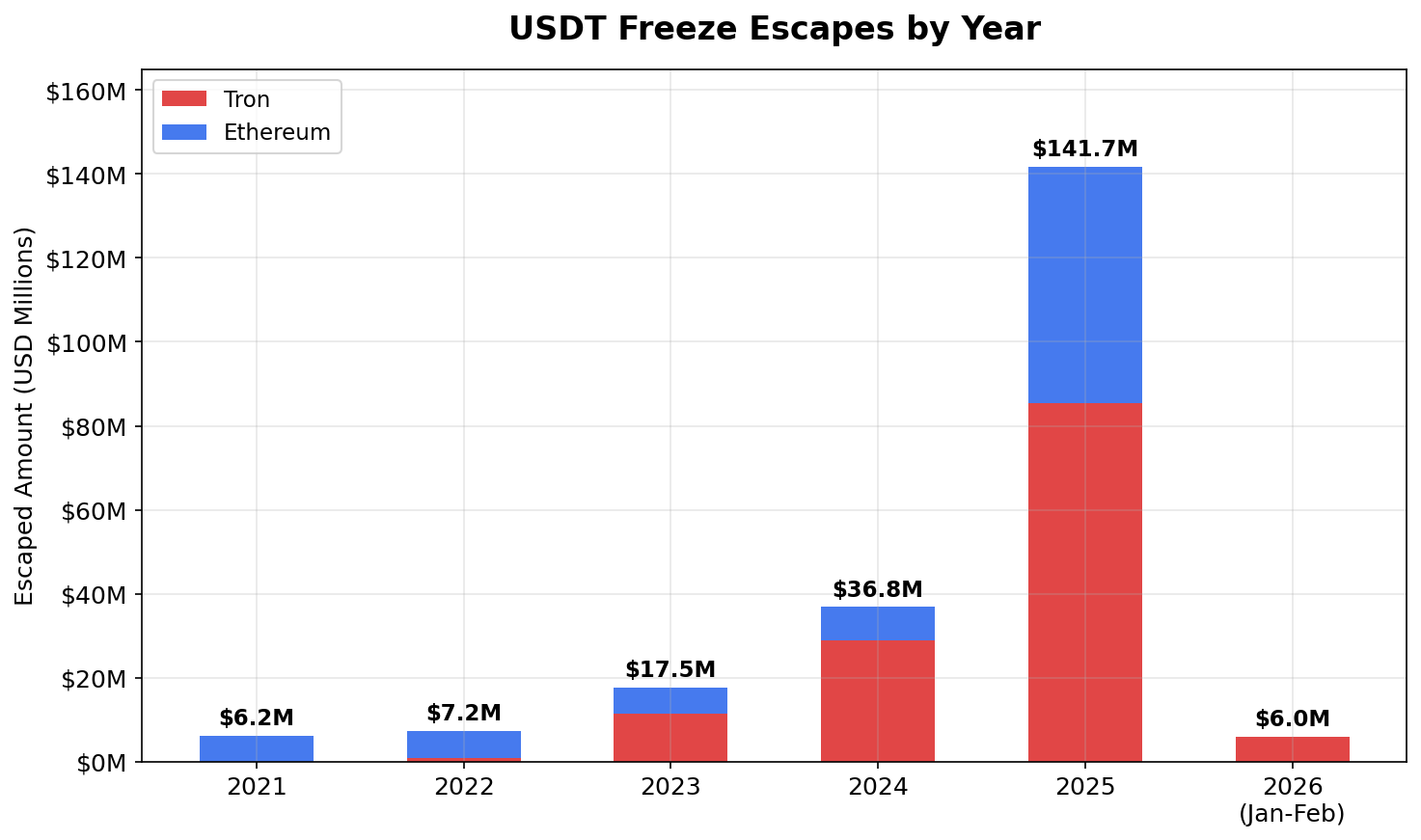
Two things stand out.
2025 was an inflection point. $141.7 million escaped — more than all prior years ($67.7 million) combined. The escape rate climbed from ~5% to over 6%.
Tron’s escape problem grew dramatically. In 2022, Tron escapes totaled under $1 million. By 2025: $85.3 million. A roughly 95x increase in three years.
The Top Escapes
Case 1: $37.3 Million in Under 6 Minutes (Tron, June 2025)
The largest escape in our dataset. Target: TD3bLbnVvcvucnJm8uhvVYGwinUzFUFgud.
| Time (UTC) | Δ | Event | Transaction |
|---|---|---|---|
| Jun 5 23:06:24 | — | Proposal submitted | 0b2e98202e95f71e269c20b1fd96a6e8e9e062d984c4b3029d02b9826718e95b |
| Jun 5 23:10:06 | +3m 42s | Escape: $37,300,258.51 | a5dfb473bd7df6fa4b787882a3240c9eab2842da546ae89a963002a201aacd16 |
| Jun 5 23:12:06 | +5m 42s | Proposal executed (frozen) | 40ac372f926f4208b0ef676a28845b6a8a21f2eb5da0fd5d0a001ce21873d9cf |
One transaction, $37.3 million, out in 3 minutes and 42 seconds. Someone was watching.
Case 2: $27.1 Million on Ethereum (July 2025)
The largest Ethereum escape. Proposal #4461 targeted 0x928b8864151ee6C1E057964460bf5c7ADDbcA97f.
| Time (UTC) | Δ | Event | Transaction |
|---|---|---|---|
| Jul 26 10:54:11 | — | Proposal submitted | 0xdd1516cdfd65c03b9808bf4b09521dc14187cd01597aa42735d614b98822f777 (Etherscan) |
| Jul 26 10:59:23 | +5m 12s | Escape: $27,121,615.88 | 0x7848e9c1f8c3a1d775c23549ba756bd78952033bb51718c53d6c346d1ce12f76 (Etherscan) |
| Jul 26 11:08:11 | +14m 0s | Proposal executed (frozen) | 0x3e8af13de42483ea7c3f755cd36ee712019d31fe858f49b7f6ed9338f961b599 (Etherscan) |
Case 3: The Serial Escaper — $15.3M Across 4 Proposals in 2 Days
Between July 28 and 29, 2025 (UTC), four Ethereum proposals targeted different addresses. Each escape: almost exactly $3.83 million. One transaction each. Response times: 12 to 24 seconds.
Proposal #4472 — Target: 0xfFc99C05f09AAF22F380D6D531EBec0489751D70
| Time (UTC) | Δ | Event | Transaction |
|---|---|---|---|
| Jul 28 19:20:47 | — | Proposal submitted | 0x5ecc0fc851fbb2dd6f8c6f023d3a49a6500985515c3b6b1a6ec581808ebb6051 (Etherscan) |
| Jul 28 19:21:11 | +24s | Escape: $3,827,986.90 | 0xc3decff1cab66d18b47f6c04a5116a1b155efbc48e44bdbd40055fd9b9350975 (Etherscan) |
| Jul 28 19:22:59 | +2m 12s | Proposal executed (frozen) | 0xa80e1d4c6e5d7a0afcc67b9cc9097c6e628bdda51993e768ce1bae86946314ae (Etherscan) |
Proposal #4477 — Target: 0x1DD5D0257c31a25Be532dc638784e53277AaBCBb
| Time (UTC) | Δ | Event | Transaction |
|---|---|---|---|
| Jul 29 13:04:11 | — | Proposal submitted | 0xfd7ab08b30d584eafd7e3d45f146e5281c0db410809419429a0ed794e9d5ef21 (Etherscan) |
| Jul 29 13:04:35 | +24s | Escape: $3,827,956.90 | 0x629766a5b0aabb1fcb7c841b3c9c54fa8e27a84de230e6f8e77e9bc10bc15089 (Etherscan) |
| Jul 29 13:04:59 | +48s | Proposal executed (frozen) | 0x08eb0abc3afb7c35d8a873a5dcc3fa5efe61d1c84b4ff9ab9de8e1806c97b3e5 (Etherscan) |
Proposal #4480 — Target: 0xb74999968A77B4b5Dbedc12f1b7eC0851934f93A
| Time (UTC) | Δ | Event | Transaction |
|---|---|---|---|
| Jul 29 19:43:11 | — | Proposal submitted | 0x53b323493b961c2d616031635a233f1316d46ec2f1d2720034493a8922c8cc5d (Etherscan) |
| Jul 29 19:43:23 | +12s | Escape: $3,827,941.90 | 0x6949e7ad9cb3a8abc23c25afeb2cd005d5663eaf57aa475e244efd59752f2d84 (Etherscan) |
| Jul 29 19:44:11 | +1m 0s | Proposal executed (frozen) | 0xd11d26c86afc9794ffa871539a6e3fd5ebd63f0b56c7f830febed86a5c58180f (Etherscan) |
Proposal #4482 — Target: 0xe15709BfB1b3C1bD8a29Ffe87804bB6767308901
| Time (UTC) | Δ | Event | Transaction |
|---|---|---|---|
| Jul 29 19:59:11 | — | Proposal submitted | 0xcb4898412b6e0fede0e421e17a2f50c4f826cd98b1708ca9bc0e496cf53a1058 (Etherscan) |
| Jul 29 19:59:23 | +12s | Escape: $3,827,941.90 | 0xdc9530ac9f00c3df1d1940a91f1f8106ded0c8e05d8e43ad6fd92d11303ce51d (Etherscan) |
| Jul 29 20:00:35 | +1m 24s | Proposal executed (frozen) | 0x37653d15e79ae4b53fd2280783a54f560835ba6c2eeba862a98b11297c66f327 (Etherscan) |
Different destination addresses each time. But the amounts are nearly identical — decreasing by exactly $15 or $45 per hop (transaction fees). Response times of 12-24 seconds don’t leave room for manual intervention. This is a bot. One actor, cycling funds through disposable wallets, auto-firing the moment a freeze proposal appears on-chain.
Case 4: The 77-Hour Window — $12.7M (Ethereum, November 2025)
Three proposals targeting three addresses, all submitted within seconds. 77 hours before execution. Three different actors drained funds across multiple days.
0xE5264B95A492F88bEc7C9861a43B55E12488c845 and 0xF92AD00A9185cCf48364e285b875D4E84aA8C917 share a common destination (0xD7873Ecfe0328aB85F4e4459259278929f469a64) — likely the same entity. 0x7c879169f739AAbFD13A1E4842ed201393311708 scattered $4.25M across 15 addresses ($100 to $500,000 each) over 2+ hours — classic layering behavior.
Escape Patterns
How do escapers move funds? We categorized all 449 events:
| Pattern | Events | Amount | Description |
|---|---|---|---|
| Single transfer | 229 (51%) | $116.6M (54%) | One transaction, clean exit |
| Multi-transfer (2-4 txs) | 153 (34%) | $40.2M (19%) | Small number of splits |
| Scatter (5+ txs) | 67 (15%) | $58.6M (27%) | Many small transfers, layering |
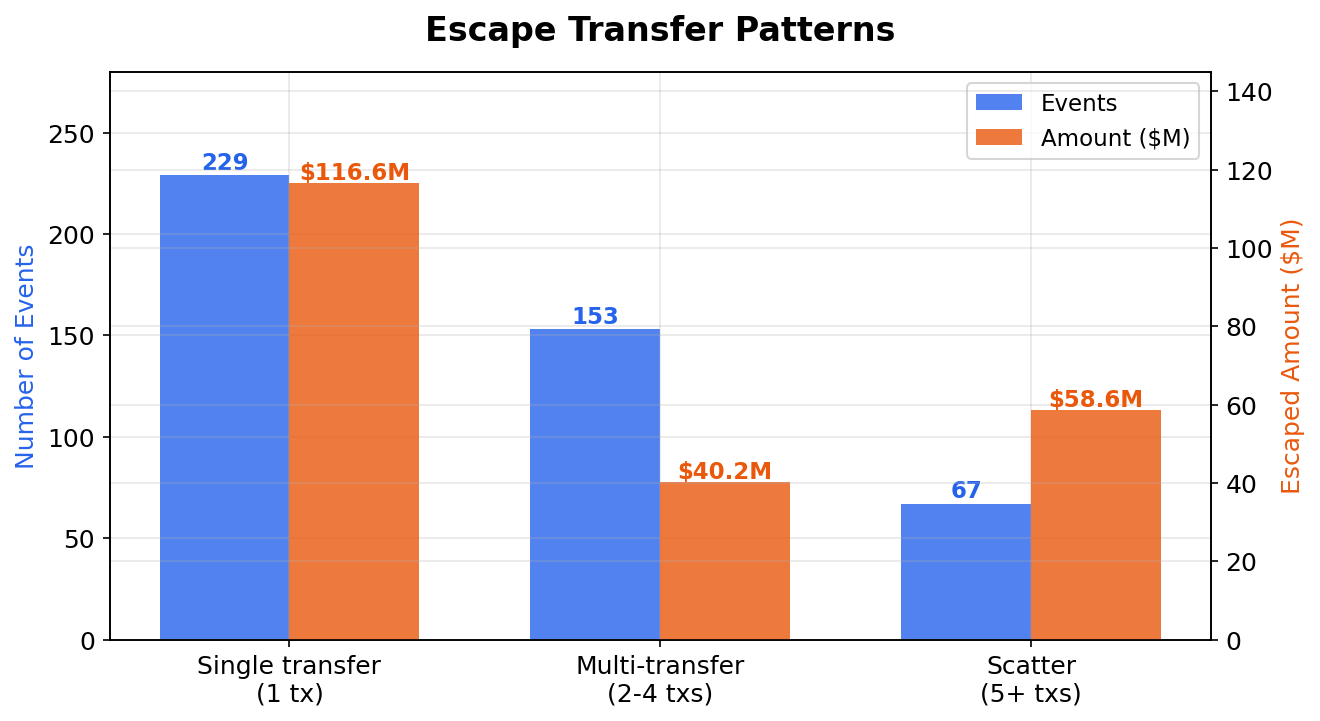
Most escapes are single-transfer events. Makes sense — if you know a freeze is coming, the fastest exit is one big transaction. The scatter pattern, though less common, averages $875K per event versus $509K for single transfers.
By Amount
| Bracket | Events | Total |
|---|---|---|
| < $1K | 50 | $12K |
| $1K - $10K | 71 | $275K |
| $10K - $100K | 160 | $6.7M |
| $100K - $1M | 133 | $44.1M |
| $1M - $10M | 32 | $88.0M |
| $10M+ | 3 | $76.4M |
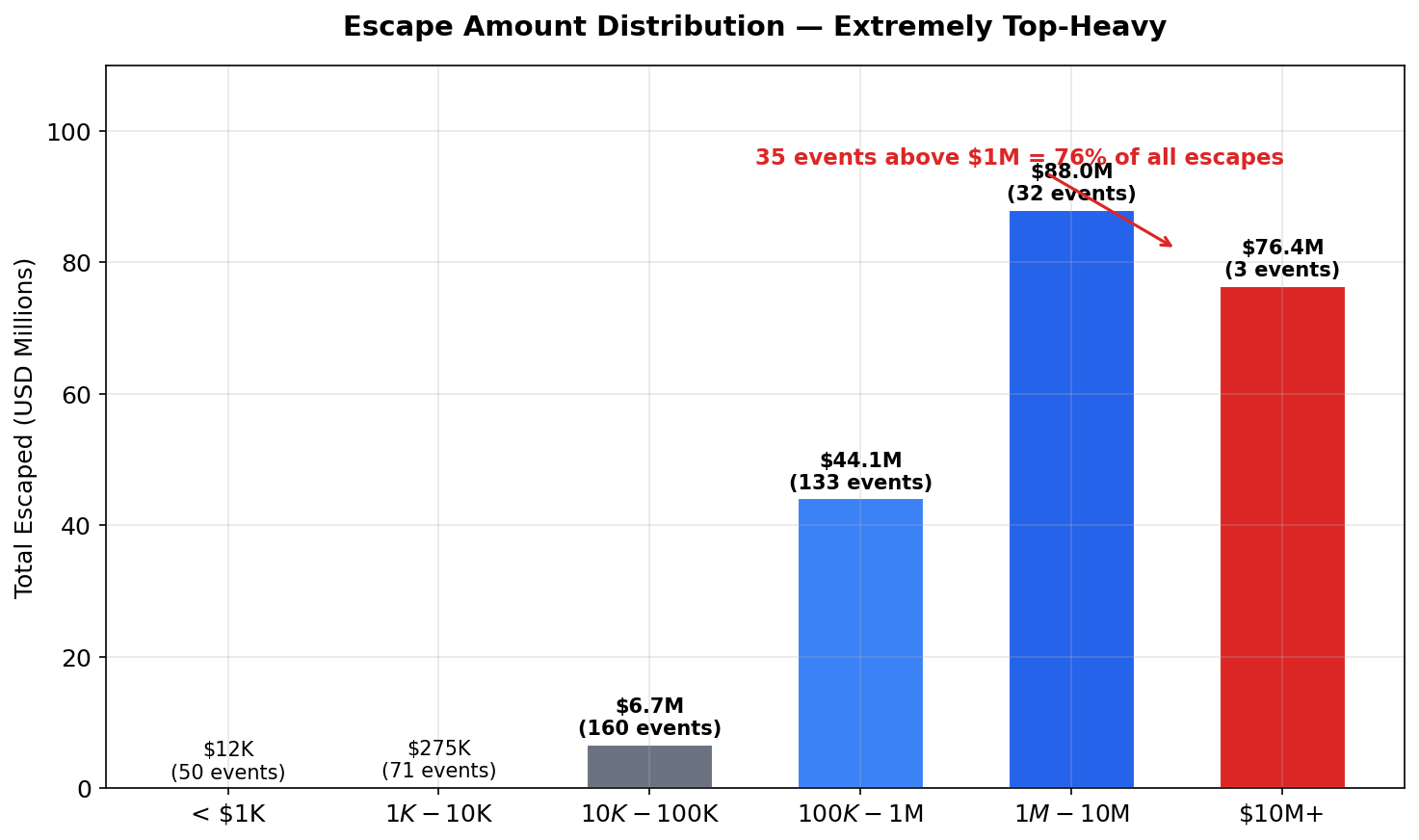
Extremely top-heavy. 35 events above $1M account for $164.4 million — 76% of the total. The three $10M+ escapes alone: $76.4 million.
How Fast Do Escapers React?
We measured the time between proposal submission and the first escape transfer for all 449 events:
| Metric | Time |
|---|---|
| Fastest | 3 seconds |
| Within 1 minute | 18 events |
| Within 5 minutes | 54 events |
| Within 15 minutes | 105 events |
| Within 1 hour | 204 events (45%) |
| Median | 77 minutes |
| 75th percentile | 5.6 hours |
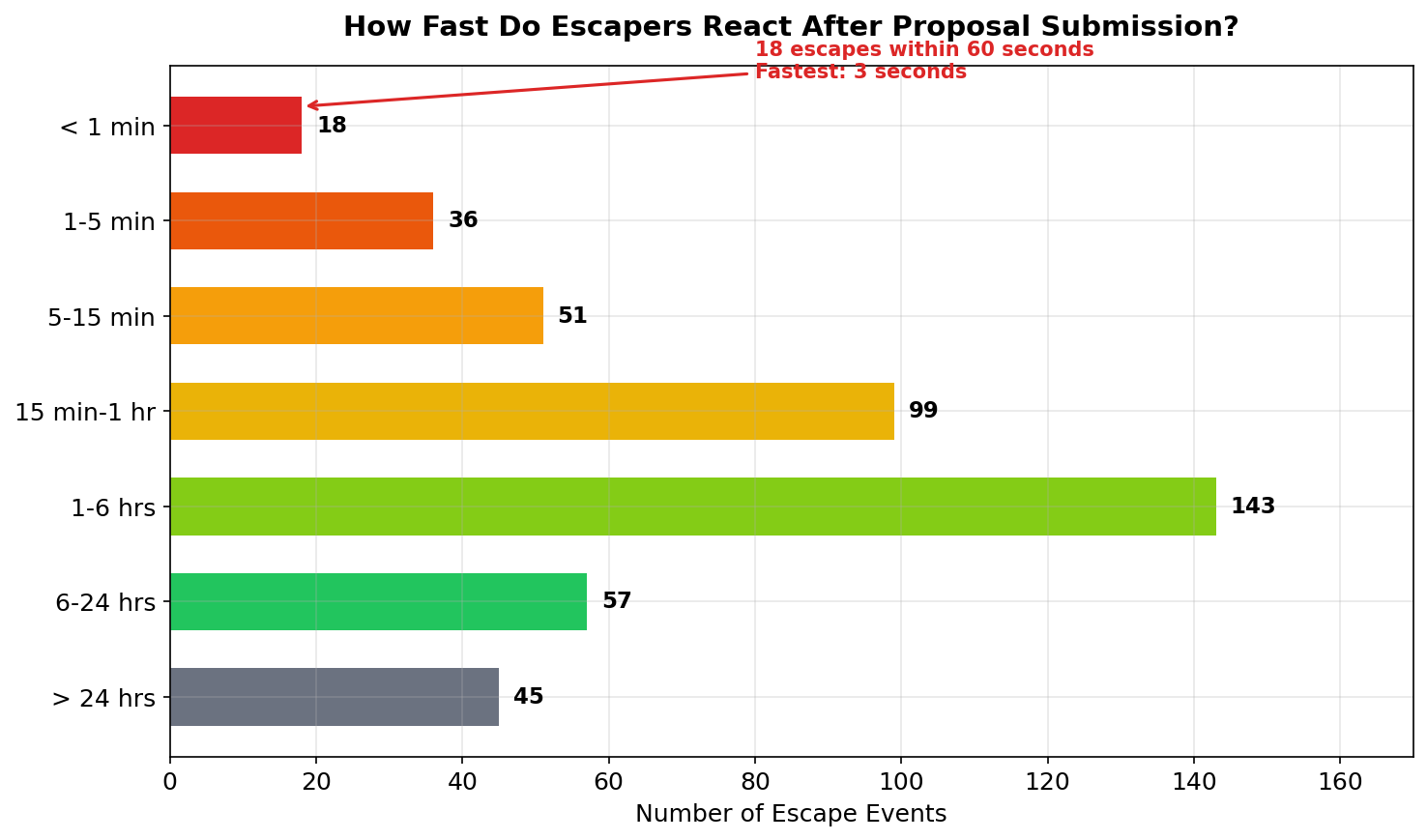
18 escapes within 60 seconds. The fastest: 3 seconds. That’s not a human refreshing a block explorer. That’s a bot monitoring the multisig contract for submitTransaction() calls, auto-firing the moment a freeze appears.
Nearly half of all escapes (204 out of 449) started within one hour. The 77-minute median suggests many actors check their exposure regularly, even without automated tools.
Putting It in Context
Tether has pointed out — and they’re right — that freeze escapes need context. $215 million against $2.7 billion+ successfully frozen puts the escape rate at roughly 7.4% by value. Over 92% of targeted funds were successfully frozen.
The freeze gap is also an inherent trade-off. Tether’s multisig model prevents any single party from unilaterally freezing funds. PeckShield called this “an operational issue” rather than a smart contract vulnerability, suggesting that bundling freeze requests and signatures into single transactions could narrow the window.
Still. $215 million. The trend is moving in the wrong direction — 2025 set records for both total escapes and escape rate. And as the serial escaper in Case 3 shows, purpose-built tools to exploit the freeze gap already exist.
What This Means for Compliance Teams
If you rely on USDT freezes as an enforcement tool, these numbers are worth knowing.
The freeze gap is a known vulnerability. Anyone monitoring the Tether multisig can detect proposals before execution. For high-value targets, assume the target is monitoring too.
Speed matters. 45% of escapes happen in the first hour. Every delay in execution increases the risk.
Watch for patterns. Single transfers to fresh addresses. Scatter patterns across many wallets. Near-identical amounts across multiple proposals. These signal an actor gaming the system.
BlockSec’s USDT Freeze Tracker and Phalcon Compliance give compliance teams real-time visibility into freeze proposals and fund flows. When a $37 million escape can happen in under 6 minutes, you need to be watching.
Methodology
- Data source: On-chain data from Ethereum and Tron, processed via the BlockSec USDT Freeze Dashboard.
- Period: November 28, 2017 – February 14, 2026.
- Scope: All 8,310 executed
addBlackListproposals across both chains. - Escape definition: USDT transfers where
from_address= proposal target address, occurring between proposalsubmit_timeandexecute_time. Address-poisoning transfers excluded. - Cross-validation: All results independently verified using both Python and Go, with matching outputs.
- Limitation: Earlier versions of our Tron transfer data contained non-USDT TRC20 transfers from a legacy API endpoint. All Tron addresses have since been re-fetched using the corrected API, and the data used in this analysis reflects the cleaned dataset.